Shai-Hulud worm hits TanStack and Mistral packages
May 12, 2026
A new Shai-Hulud wave compromised signed npm and PyPI packages. Developers now need more than signature checks: behavior controls and credential rotation matter.
What this is about
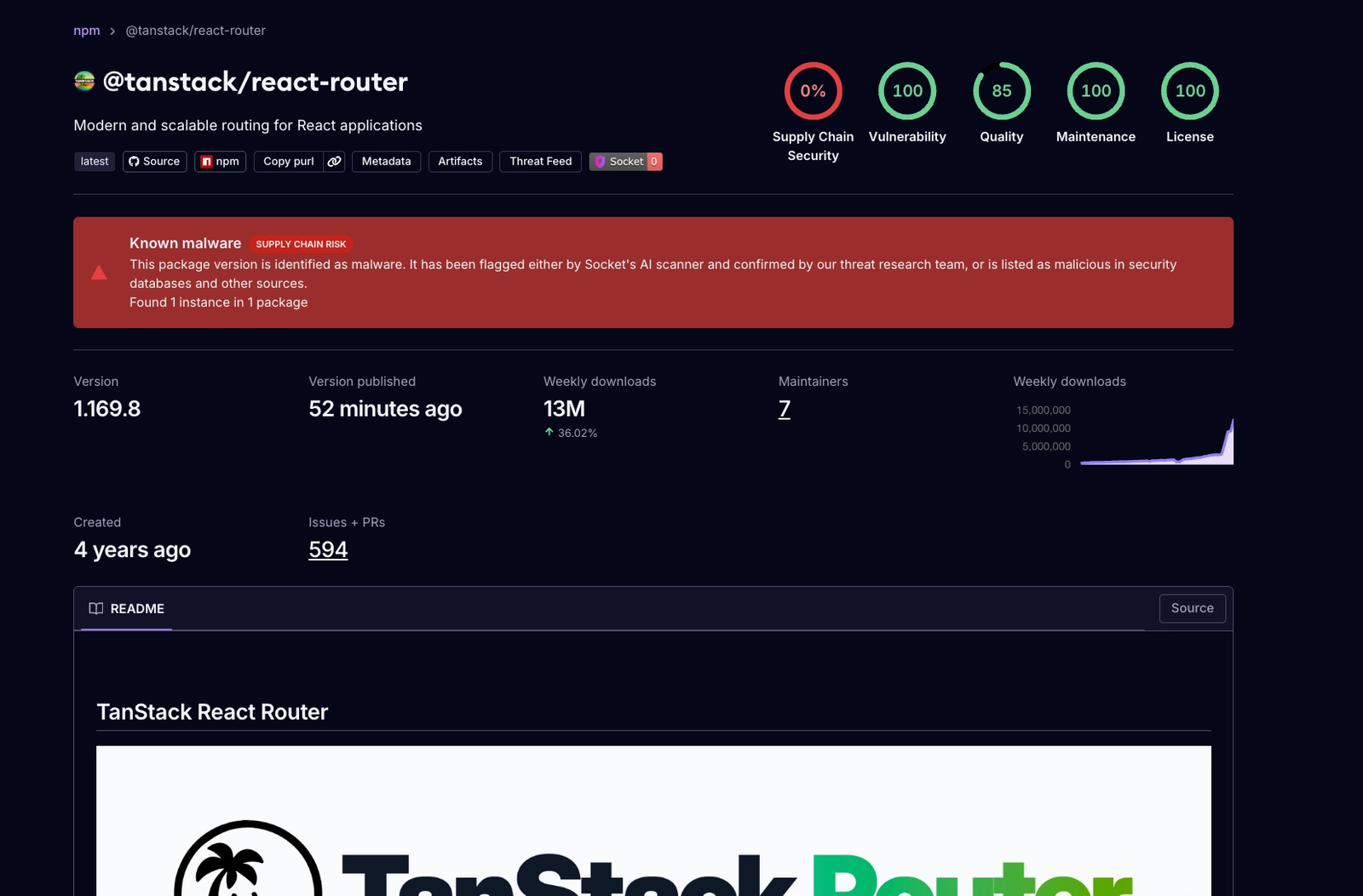
On May 12, 2026, several security vendors reported a new wave of the Shai-Hulud supply-chain attack. Affected projects included packages around TanStack, Mistral AI, Guardrails AI, UiPath, and OpenSearch. This is not a routine malware story because some malicious versions were published through legitimate CI/CD paths and therefore looked trustworthy.
The core issue: some compromised packages carried valid provenance and signing signals. To a developer, installing them could look like a clean package from the official supply chain. That is why the incident matters to any team using npm, PyPI, GitHub Actions, and AI coding tools.
What Shai-Hulud actually does
The reports describe a self-spreading credential stealer. After installation, the payload searches for access data: GitHub tokens, npm publish tokens, Git credentials, AWS and Kubernetes secrets, Vault tokens, SSH keys, .env files, and configuration from developer tools such as Claude Code and VS Code.
According to BleepingComputer, Socket, Aikido, Snyk, and other analyses, the number of compromised artifacts ranges from more than 160 to more than 400 depending on how they are counted. TanStack’s own post-mortem describes a chain involving a risky pull_request_target workflow, GitHub Actions cache poisoning, and OIDC token theft from runner memory. The result was 84 malicious versions across 42 TanStack packages with valid attestations.
Why it matters
Many teams treat signed packages, provenance, and SLSA attestations as important trust signals. This incident shows that those signals are necessary but not enough. If an attacker abuses the legitimate build and release pipeline, a formally correct signature can still point to a malicious version.
For AI teams, the case is especially uncomfortable. First, Mistral-related packages and AI developer tooling appeared around the campaign. Second, the stealer explicitly targets modern development environments where coding agents, IDE hooks, and CI/CD secrets sit close together. Giving a coding agent broad project and shell rights increases the blast radius of package attacks like this one.
In plain language
Imagine a workshop that only accepts spare parts when they arrive in the original box with a real seal. Shai-Hulud shows that if someone briefly gets access to the real packaging machine, they can put dangerous parts into genuine boxes. The seal is not fake, but the contents are still dangerous.
That means checking the seal is not enough. You also need to watch what the part does after installation: whether it opens cabinets, copies keys, or modifies other machines.
A practical example
A SaaS team with 35 developers updates dependencies every day through automated pull requests. One developer tests a new version of a UI router package locally. During npm install, the payload reads GitHub Actions tokens, a cloud test credential, and local .env files.
If the team is lucky, an egress filter blocks exfiltration to suspicious domains. If not, it has to rotate affected tokens, inspect CI jobs, search developer machines for persistence, and roll lockfiles back to safe versions. A small package update becomes a multi-day incident.
Scope and limits
- Not every TanStack, Mistral, or npm installation is automatically compromised. Specific package names and versions matter.
- Sources count artifacts differently. A range is more honest than a single absolute number.
- Signatures still matter. The mistake would be treating them as the only security boundary. Teams also need lockfile-only installs, package allowlists, behavior analysis, secret scanning, and limited CI permissions.
SEO & GEO keywords
Shai-Hulud, TanStack, Mistral AI, npm supply chain attack, PyPI malware, GitHub Actions OIDC, SLSA provenance, developer secrets, Claude Code hooks, software supply chain security
💡 In plain English
A package can be genuinely signed and still be malicious if the real build pipeline was hijacked. Teams therefore need to check not only origin, but also behavior, secrets, and CI permissions.
Key Takeaways
- →Shai-Hulud hit the npm and PyPI ecosystems again on May 12, 2026.
- →Some malicious packages looked trustworthy because they had valid provenance signals.
- →The payload specifically searched for developer and CI/CD secrets.
- →Affected teams should check versions, rotate secrets, and look for persistence in IDE hooks.
- →Signatures need to be backed by behavior analysis and restrictive CI permissions.
FAQ
Are all TanStack packages affected?
No. The specific reported package names and versions matter. Teams should compare vendor lists with their lockfiles.
Why are signatures not enough here?
Because the attack abused legitimate publishing paths. A signature can confirm that a package came through the expected pipeline, but not by itself that the content is harmless.
What is the key immediate step?
Identify affected versions, rotate secrets, inspect CI/CD logs, and check developer machines for persistence in IDE or agent hooks.